this post was submitted on 30 Mar 2024
474 points (84.3% liked)
linuxmemes
21225 readers
37 users here now
Hint: :q!
Sister communities:
- LemmyMemes: Memes
- LemmyShitpost: Anything and everything goes.
- RISA: Star Trek memes and shitposts
Community rules (click to expand)
1. Follow the site-wide rules
- Instance-wide TOS: https://legal.lemmy.world/tos/
- Lemmy code of conduct: https://join-lemmy.org/docs/code_of_conduct.html
2. Be civil
- Understand the difference between a joke and an insult.
- Do not harrass or attack members of the community for any reason.
- Leave remarks of "peasantry" to the PCMR community. If you dislike an OS/service/application, attack the thing you dislike, not the individuals who use it. Some people may not have a choice.
- Bigotry will not be tolerated.
- These rules are somewhat loosened when the subject is a public figure. Still, do not attack their person or incite harrassment.
3. Post Linux-related content
- Including Unix and BSD.
- Non-Linux content is acceptable as long as it makes a reference to Linux. For example, the poorly made mockery of
sudoin Windows. - No porn. Even if you watch it on a Linux machine.
4. No recent reposts
- Everybody uses Arch btw, can't quit Vim, and wants to interject for a moment. You can stop now.
Please report posts and comments that break these rules!
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
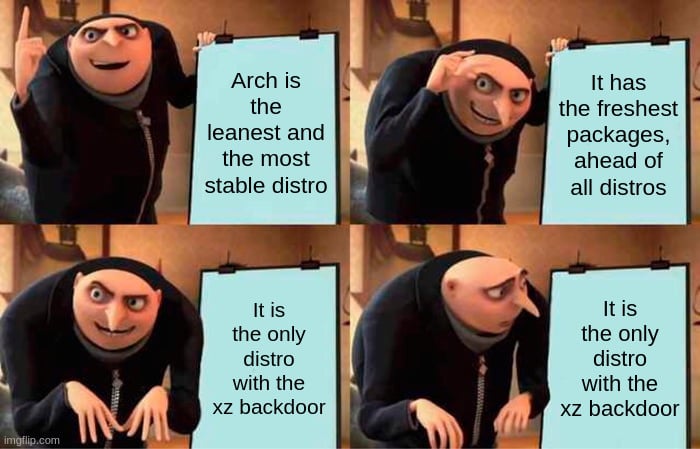
In the case of Arch the backdoor also wasn't inserted into liblzma at all, because at build time there was a check to see if it's being built on a deb or rpm based system, and only inserts it in those two cases.
See https://gist.github.com/thesamesam/223949d5a074ebc3dce9ee78baad9e27 for an analysis of the situation.
So even if Arch built their xz binaries off the backdoored tarball, it was never actually vulnerable.
I just know there is a lot of uncertainty. Maybe a complete wipe is a over reaction but it is better to be safe